Information:
- You need to Download the audio files: Language Arts DC The Official Soundtrack.wav for Part A and answer ALL questions.
Hint: Use Sonic Visualiser or Audacity
Part A:
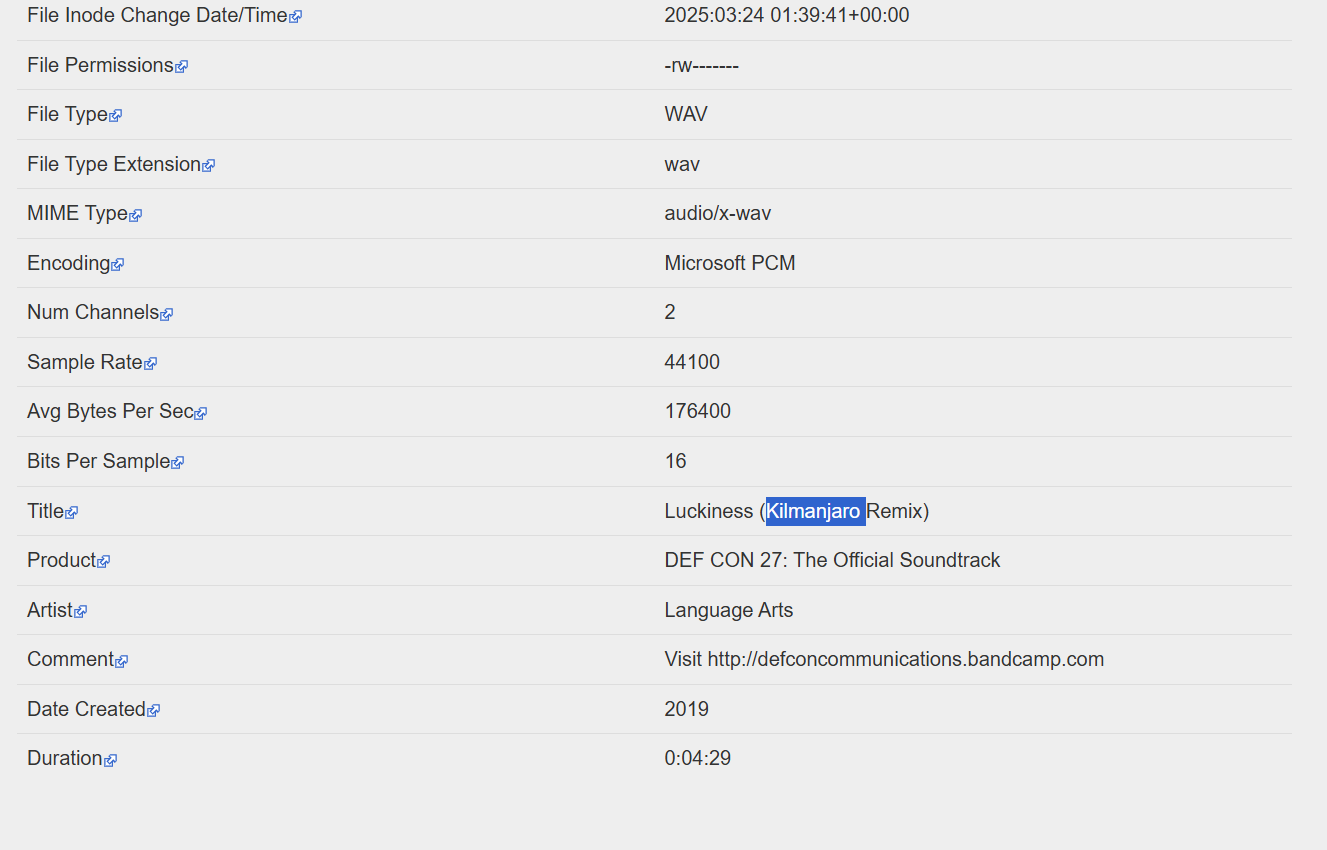
Question 1: Who remixed the song?
Answer: Kilmanjaro
Way to Solve:
Step 1: You can upload the "Language Arts DC The Official Soundtrack.wav" file to exif.tools to view the metadata, as you can get the FLAG in the title.
Question 2: What link is hiding in the music?
Answer format: *****://****.**/***********
Answer: https://voca.ro/imPgJC013AW
Way to solve:
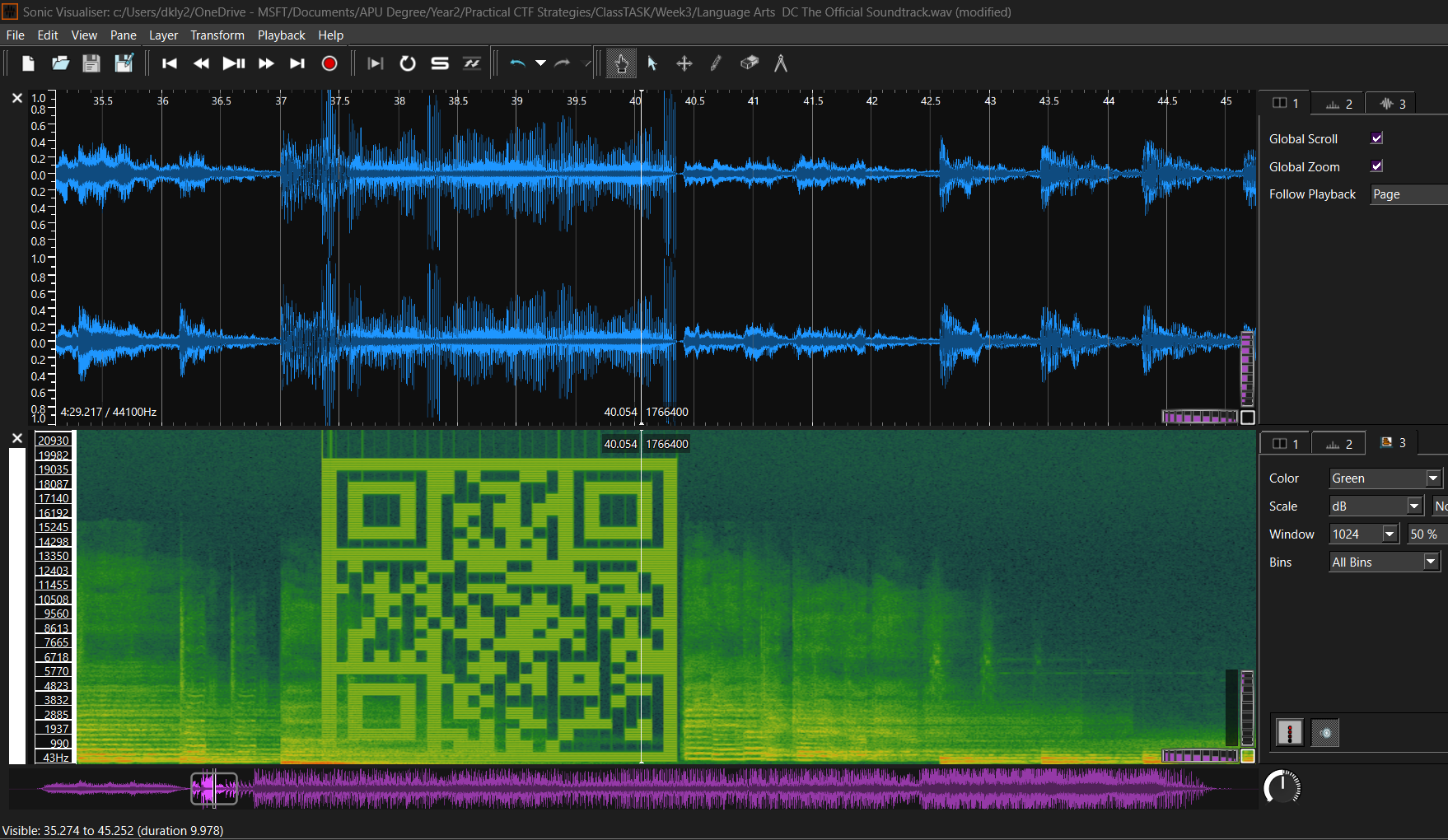
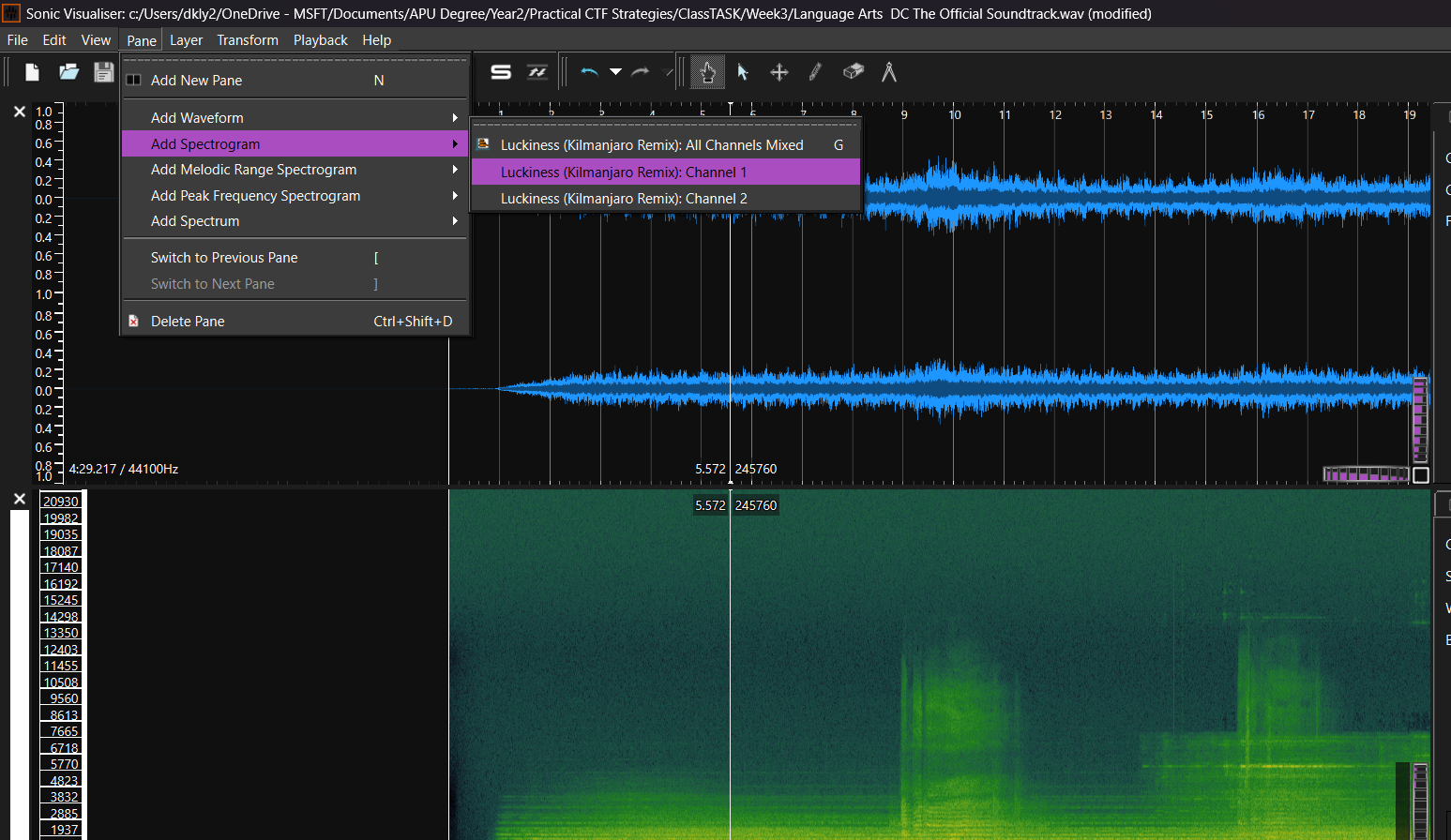
Step 1: Open your Sonic Visualiser, and import the "Language Arts DC The Official Soundtrack.wav".
Step 2: In the Sonic Visualiser, go to Pane > Add Spectrogram > Luckniess (Kilmanjaro Remix): Channel 1.
Step 3: Once enable the "Spectrogram", you can start finding the hidden flag (Qr Code).
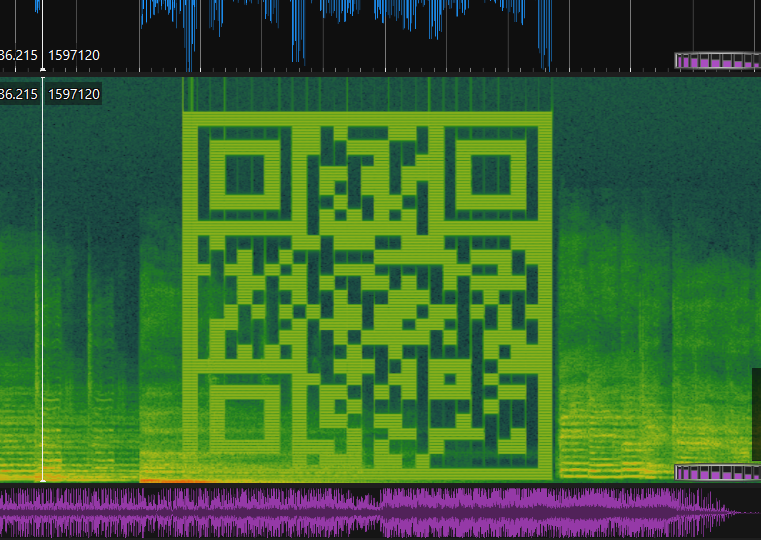
Step 4: At 36 Seconds of the "Language Arts DC The Official Soundtrack.wav", you will able to see the hidden QRcode, scan it. That's the flag.
Question 3: Listen to the audio. What does the found audio convert into?
Answer format: ***** ****
Answer: morse code
Question 4: What link is hidden in the audio after converting?
Answer format: *****://********.***/********
Answer: https://pastebin.com/LZKTB4ET
Way to solve Questions 3 & 4:
Step 1: Import the "Vocaroo imPgJC013AW.mp3" into the Sonic Visualiser.
P/s: I know you will be thinking hmm, where do I get this file ^_^. Did you still remember the QR Code you scanned at Q2? That's is the files.
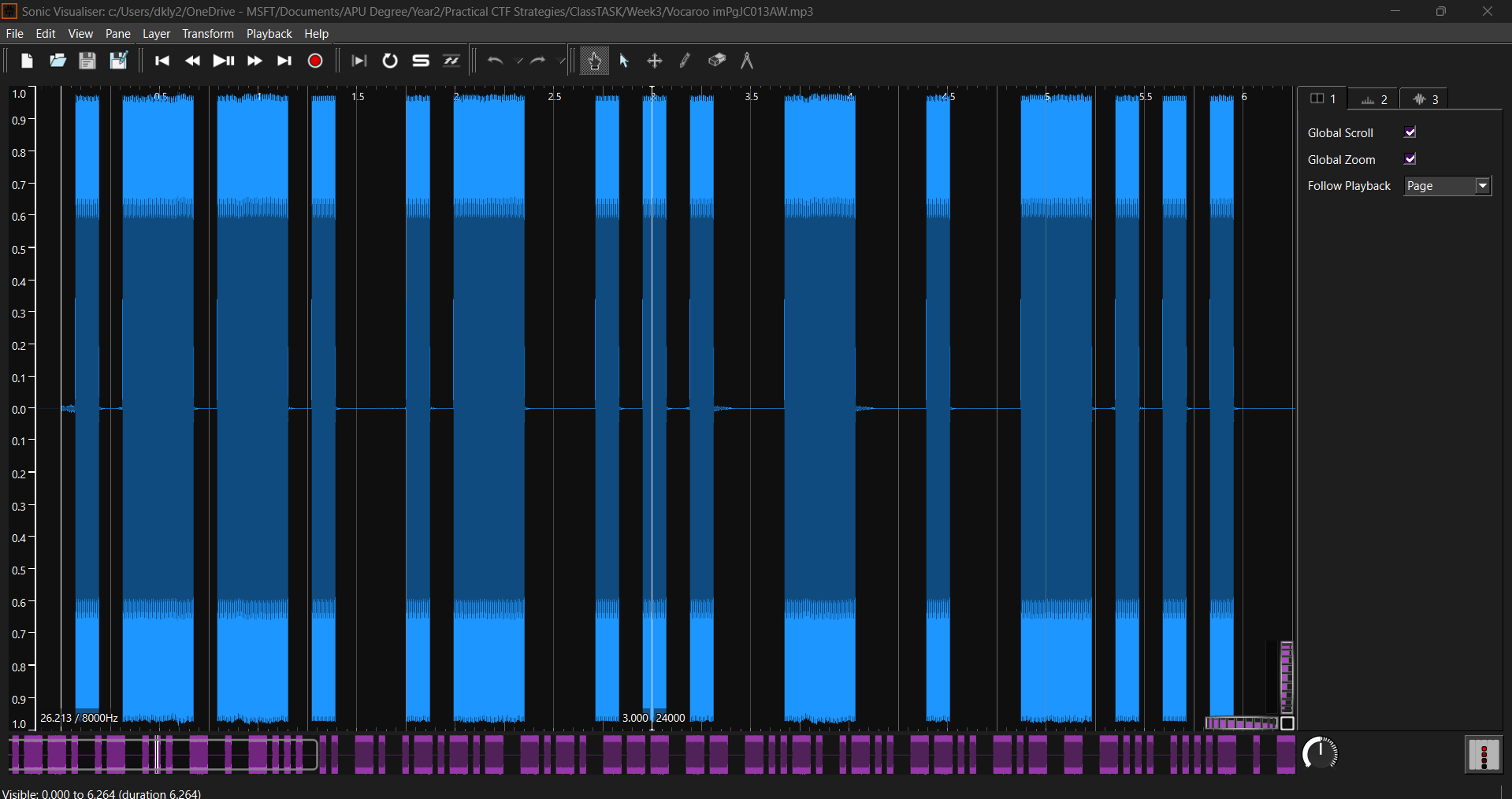
Step 2: As you can see in there the pattern looks familiar. It is Morse Code. So to change to readable text you may use Morse Code Translator to decode.
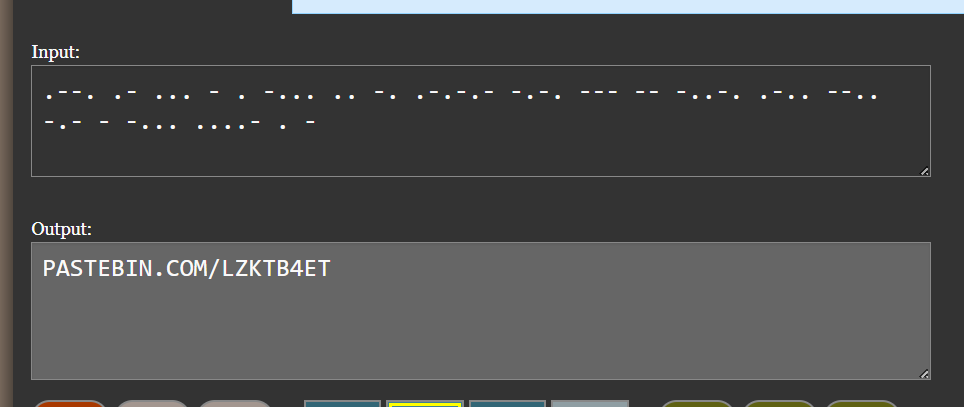
Until here, you have finished all questions/challenges in Part A. Let's move on to the Part B.
Part B:
Question 5:
Title: スター
Description: スタースタースタースタースター私はスターステガノグラフィーです
Attached file: b7acc43c15ed268a1bcb81b528e8a419.mp3
Way to solve:
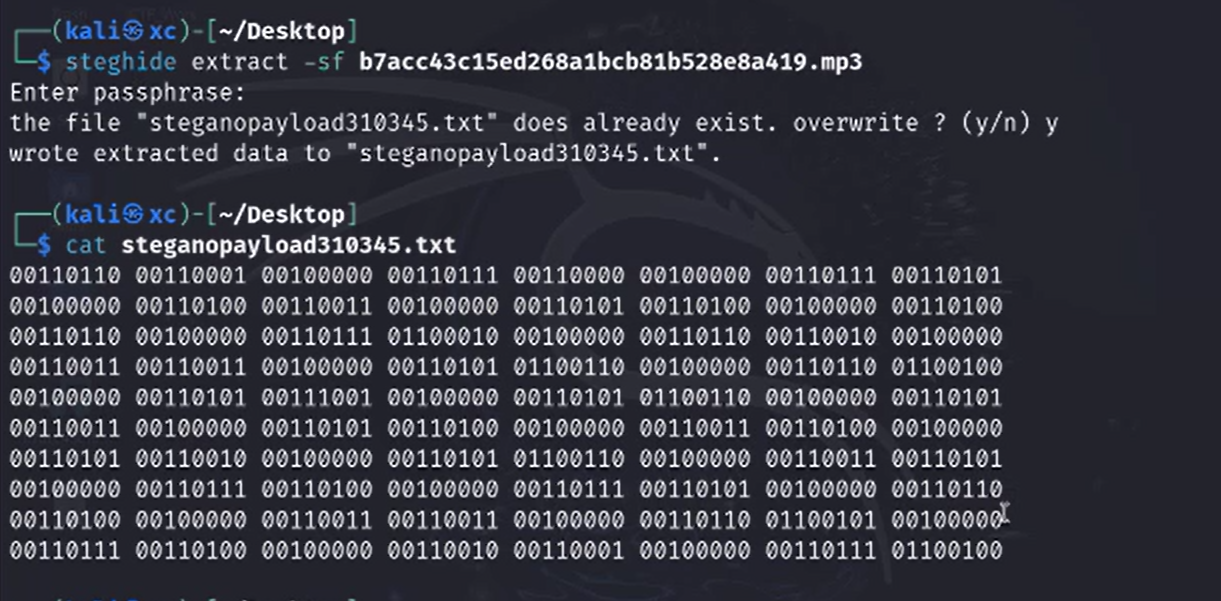
Step 1: Use the command "steghide -extract -sF b7acc43c15ed268a1bcb81b528e8a419.mp3" in your Kali Linux. It will ask you to key in a passphrase, so how do we get the key? The passphrase key is actually given in the questions, by translating the "スター" into English is "star". Then, you will get a text file named "steganopayload310345.txt". To read the file, you may use "cat steganopayload310345.txt".
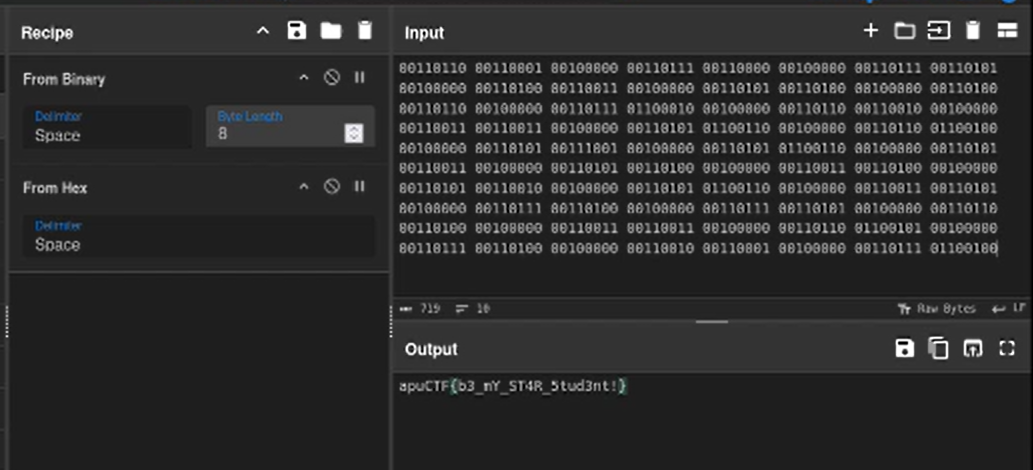
Step 2: As you can see, we got a binary text in the "steganopayload310345.txt" file. So, let's decode it by using CyberChef tools.
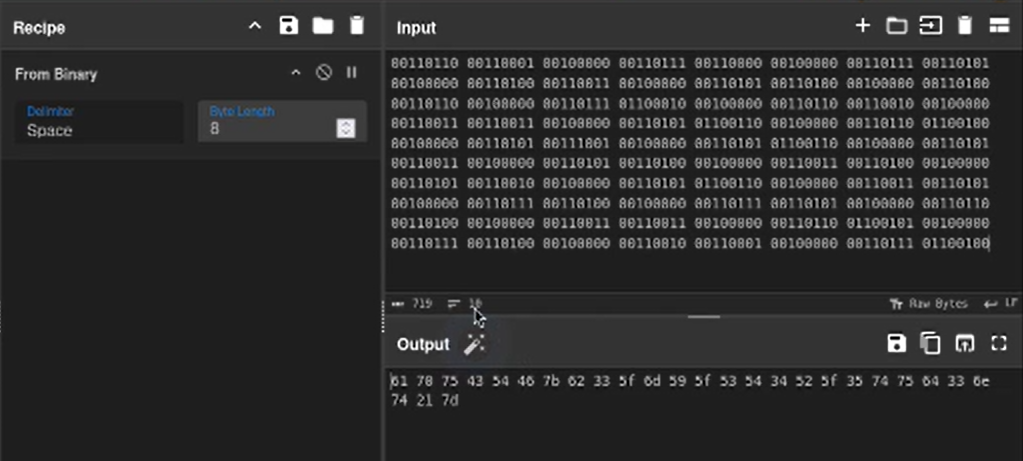
Step 3: Opps, what next? You still did not get your flag! Don't worry, this is a HEX-encoded. Let's use the function HEX decoder in the CyberChef to decode it. You will now get your FLAG!
Congratulations! You have successfully completed all the tasks in both Part A and Part B.
Throughout this class task, you utilized various tools, including Sonic Visualizer for audio analysis, CyberChef for data manipulation, and a Morse Code Decoder for decoding encrypted messages. Well done on applying these tools effectively!